Defending Ukraine: Early Lessons from the Cyber War
Latest Thread
- USA The Defense Autonomous Warfare Group (DAWG) concept
- Defence Q&A Trying to ID this thermal battery
- Forum Announcement Security verification
- China Air-Force People's Liberation Army Air Force(China)
- China 82 deaths in Liushenyu Coal Mine gas explosion
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
CYBINT/DNINT Cyber Intelligence,Techniques and developments
- Thread starter Bogeyman
- Start date
Parasite that Smiles: Pegasus Spyware Targeting Dissidents in Thailand
Parasite that Smiles: Pegasus Spyware Targeting Dissidents in Thailand
Parasite that Smiles: Pegasus Spyware Targeting Dissidents in Thailand
Liz Truss's personal phone that was hacked by Kremlin agents was so compromised it was locked away in a 'secure location' as experts fear top secret negotiations and private messages may have been leaked
Liz Truss's personal mobile phone was hacked by agents suspected of working for the Kremlin, The Mail on Sunday can reveal.
The cyber-spies are believed to have gained access to top-secret exchanges with key international partners as well as private conversations with her leading political ally, Kwasi Kwarteng.
One source said that the phone was so heavily compromised that it has now been placed in a locked safe inside a secure Government location.
The hack was discovered during the summer’s Tory leadership campaign, when Ms Truss was Foreign Secretary, but the details were suppressed by Boris Johnson, who was Prime Minister at the time, and the Cabinet Secretary, Simon Case.
It is understood that messages which fell into foreign hands included criticisms Ms Truss and her future Chancellor Mr Kwarteng made of Mr Johnson, leading to the potential risk of blackmail. Sources said that up to a year’s worth of messages were downloaded.
They are also believed to have included highly sensitive discussions with senior international foreign ministers about the war in Ukraine, including detailed discussions about arms shipments.
The astonishing incident, disclosed by security sources, solves the mystery of why Ms Truss was forced to change the mobile number she had used for over a decade shortly before becoming Prime Minister. The move caused anxiety among Cabinet Ministers and advisers who were suddenly unable to contact her.
A source with knowledge of the incident said yesterday that the security breach ‘caused absolute pandemonium – Boris was told immediately, and it was agreed with the Cabinet Secretary that there should be a total news blackout.
‘It is not a great look for the intelligence services if the Foreign Secretary’s phone can be so easily plundered for embarrassing personal messages by agents presumed to be working for Vladimir Putin’s Russia.’
Allies of Ms Truss said she was worried that if news of the hack leaked, it could derail her chance of claiming the Premiership, adding that she ‘had trouble sleeping’ until Mr Case imposed a news blackout.
Former Conservative Party leader and leading Russia critic Iain Duncan Smith said: ‘This is what we’re up against. Russia does this all the time. This is their sole purpose – their way to get back at us. We are all far too casual about our phones in general. Ministers should be much more careful and should not be using their personal phones for anything. I assume my private phone is being hacked.’
Shadow Home Secretary Yvette Cooper said: ‘This is extremely serious – it shows the severity of the threats from countries that would do us harm and why cyber-security needs to be taken so seriously by everyone in Government. We need to know that the Government recognises the gravity of this.’
A Government spokesman said last night: ‘We do not comment on individuals’ security arrangements. The Government has robust systems in place to protect against cyber threats. That includes regular security briefings for Ministers, and advice on protecting their personal data.’

Liz Truss's personal phone hacked by Putin's spies
One source said that the phone was so heavily compromised that it has now been placed in a locked safe inside a secure Government location.
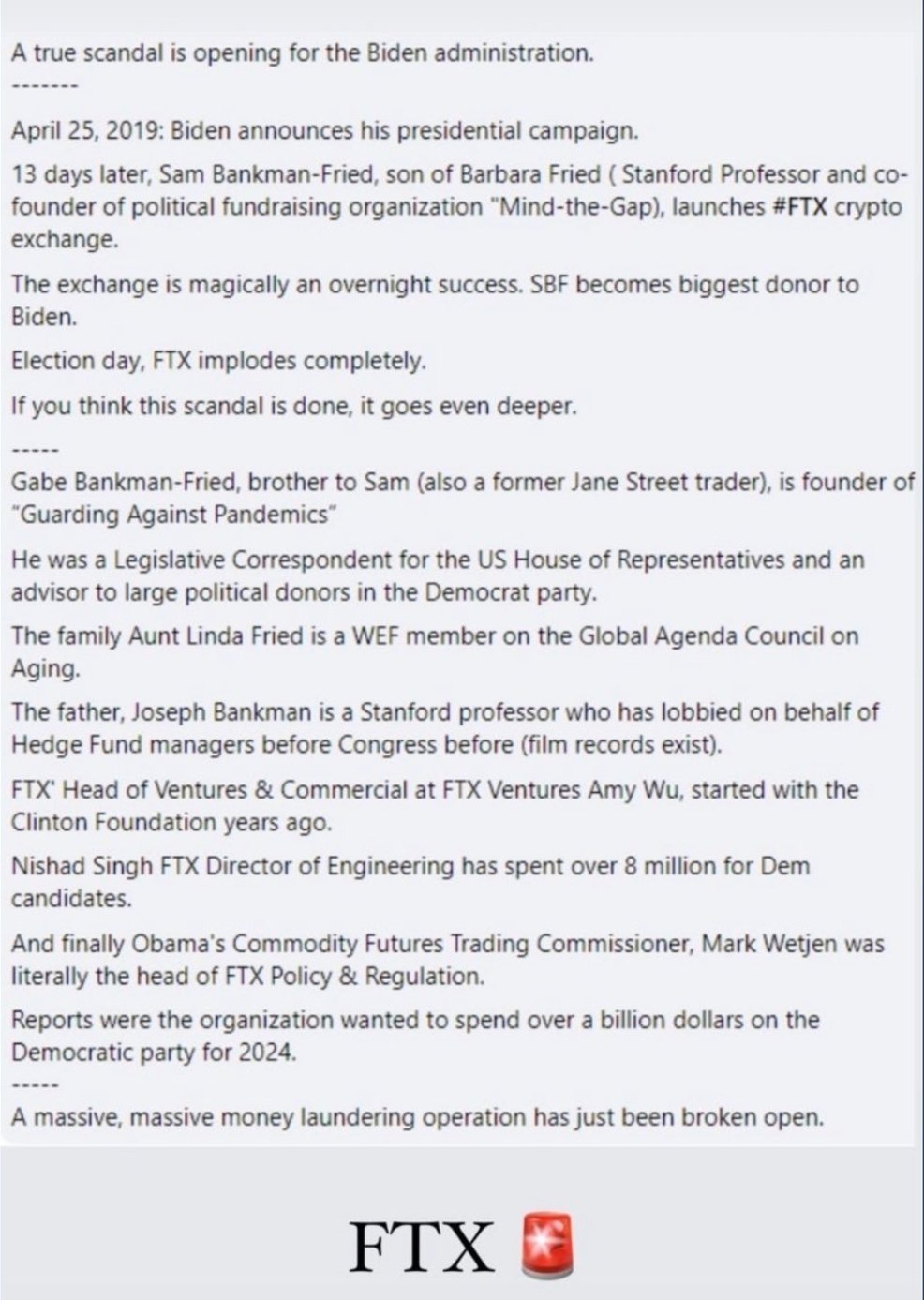
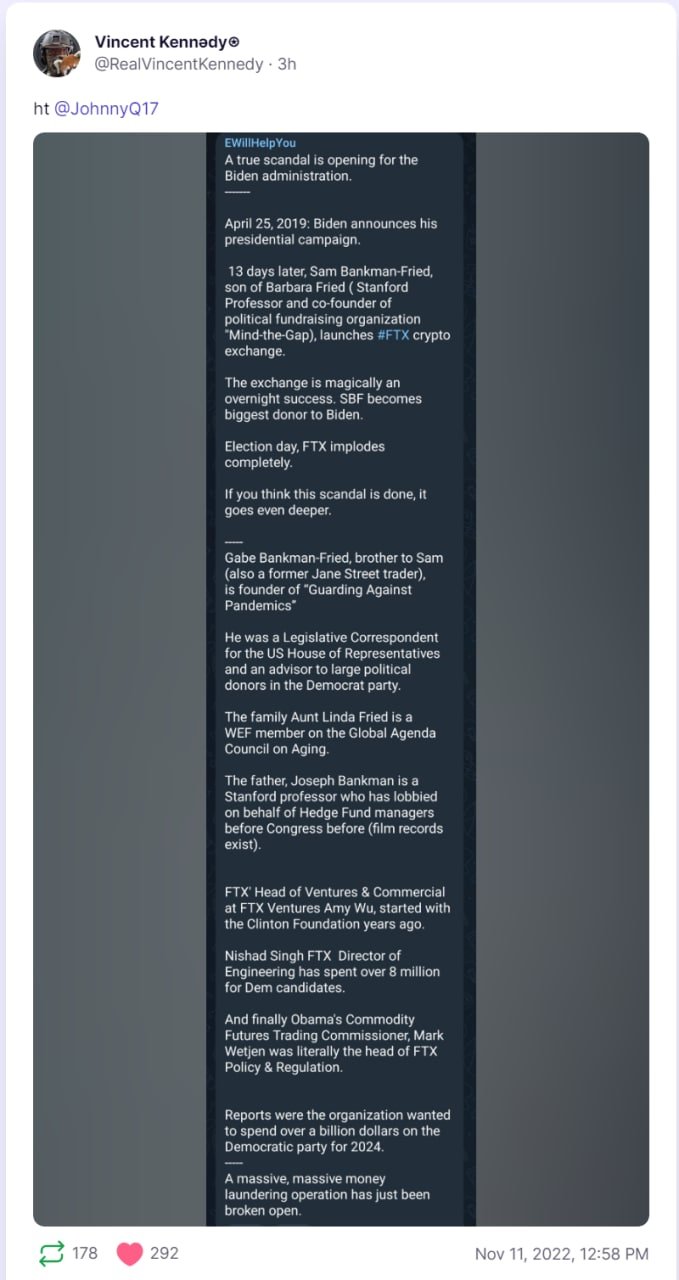
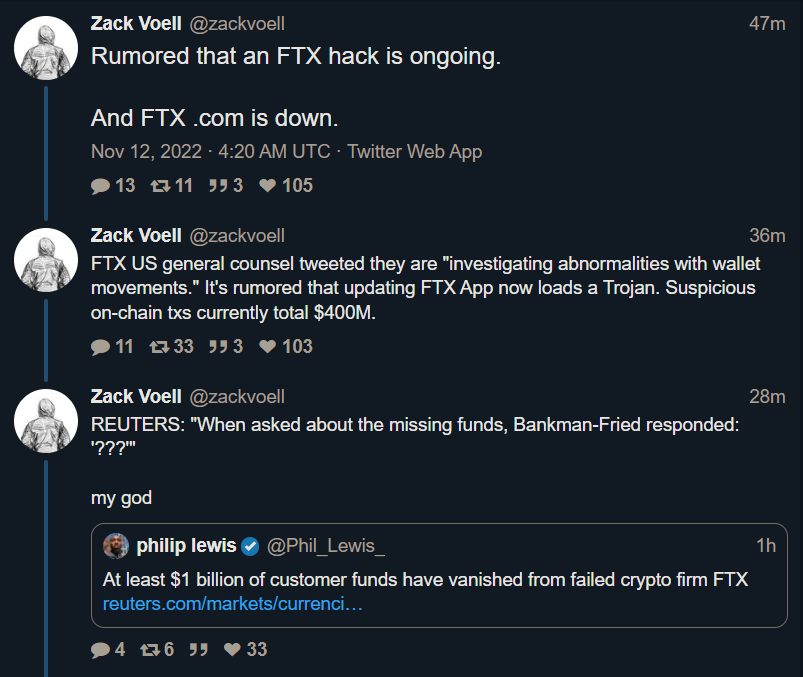
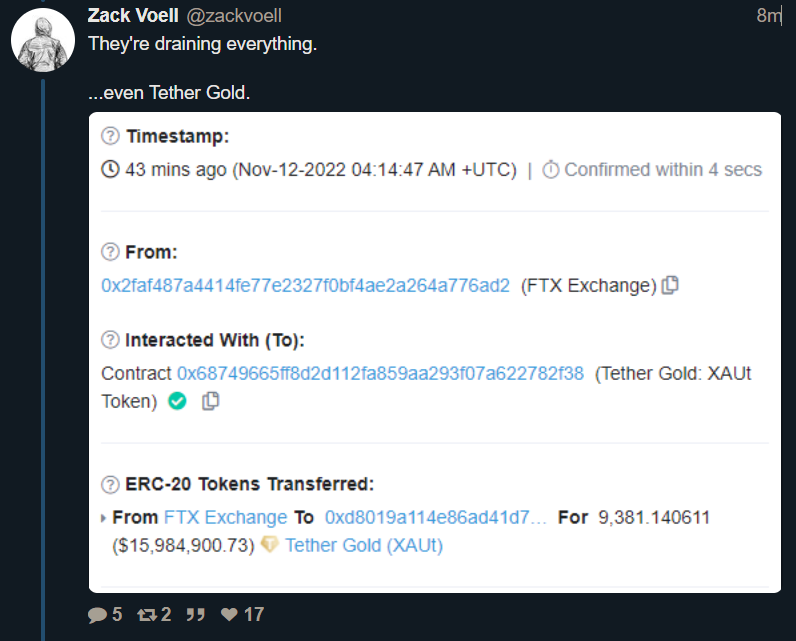
UKRAINE "MILITARY AID" FROM USA --- WAS INVESTED IN CRYPTO "FTX" BY UKRAINE!
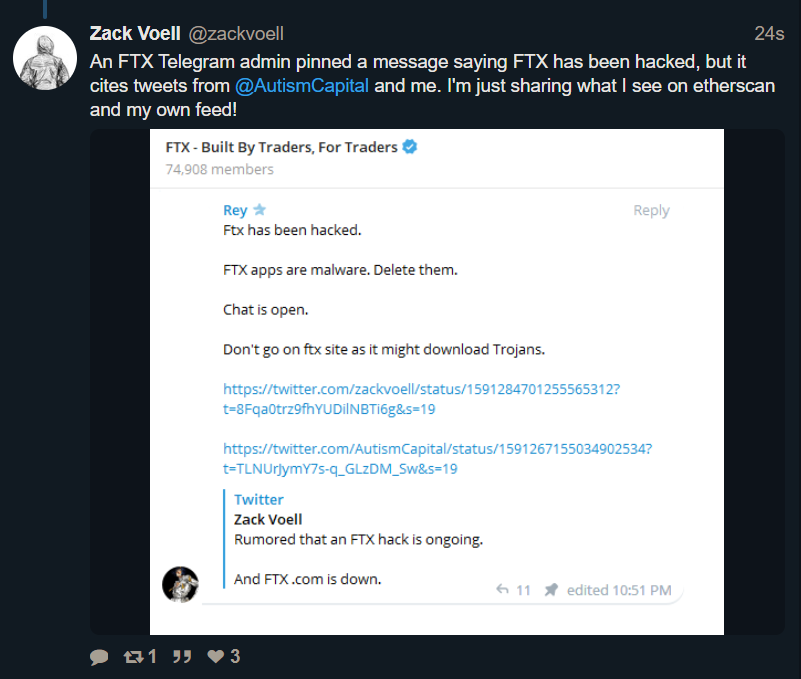
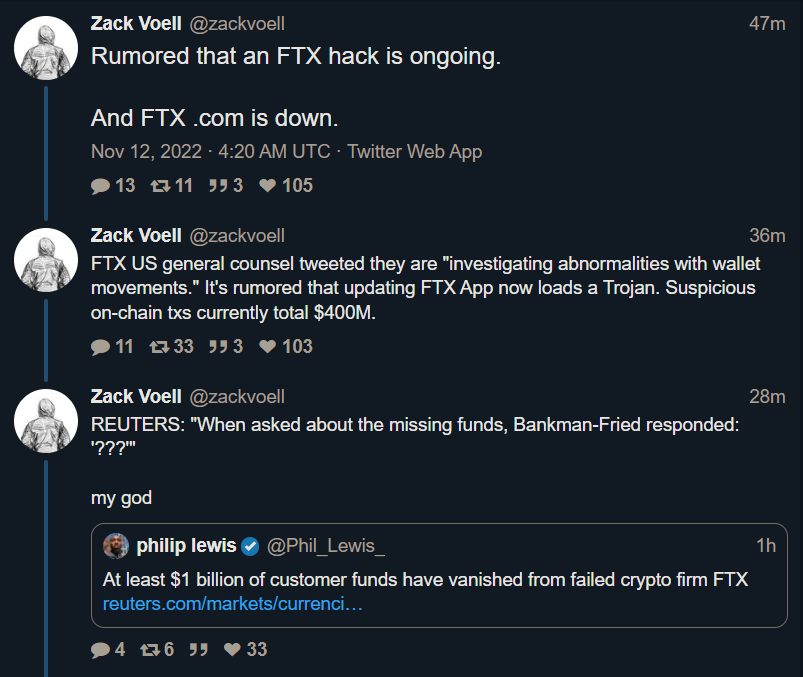
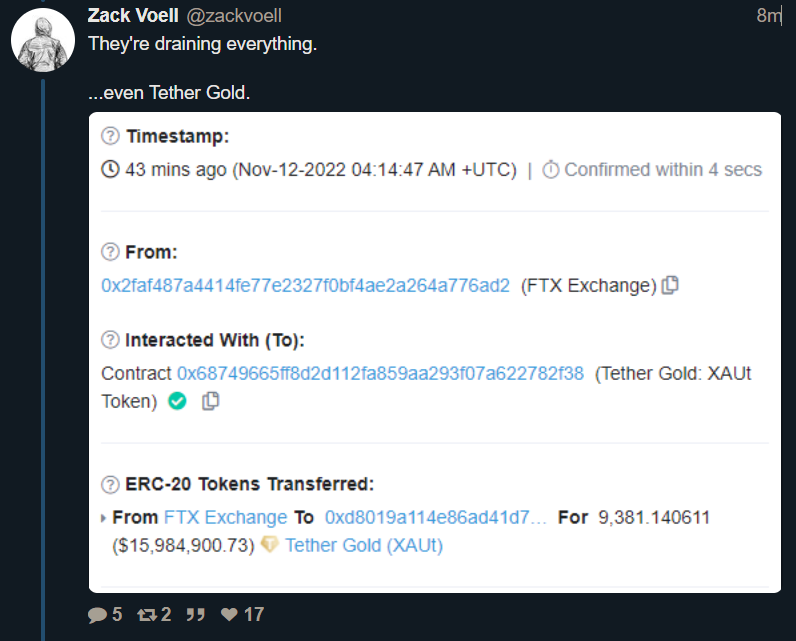
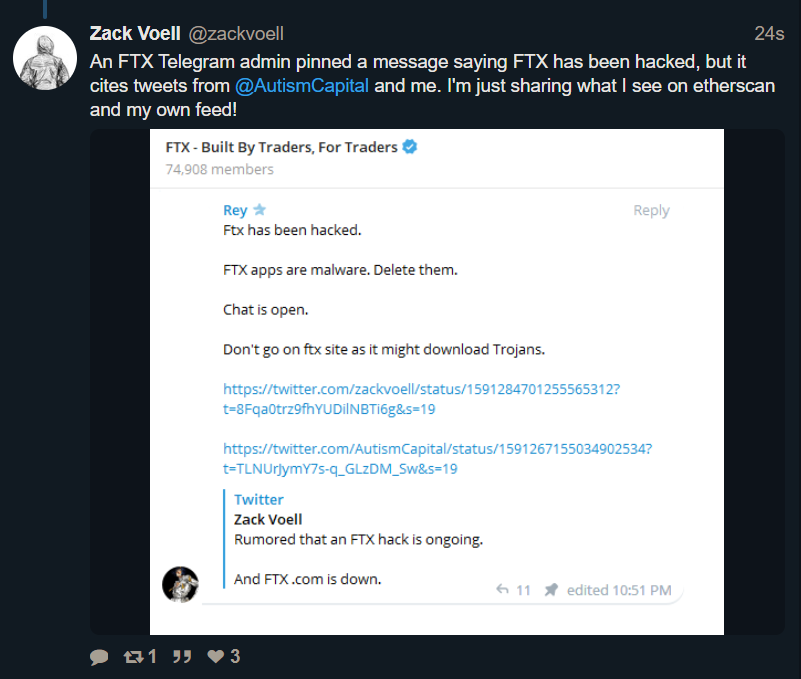
The sudden collapse of crypto exchange "FTX" and its Bankruptcy filing today, has revealed that FTX presently suffers from $10-$50 BILLION in liabilities with almost ZERO assets . . . and among those liabilities, are "investments" made by . . . . UKRAINE . . . .
At this early hour, it __appears__ that tens-of-billions in American "Military Aid" to Ukraine, which was allegedly to be used to fight Russia, was cash that Ukraine DID NOT use to fight Russia, but instead invested into FTX!
And, as you might guess from the Bankruptcy filing . . . . it now seems that all the money . . . is gone.
Yes, you read that correctly: Instead of using US Military Aid to fight Russia, Ukraine "invested" part or all of it, into FTX, and right now, it looks like all the money is gone.
Democrat Donations
Also at this early hour, it now also __appears__ that the Chief of FTX, Sam Bankman-Fried, was the #2 donor to the Democrats. He was only outspent by Soros himself!
It __seems__ Ukraine was receiving money from the US, Ukraine sent it to FTX, and FTX sent it to Democrats, who originally voted to send it to Ukraine. At this hour, it __appears__ to some observers, to be pure, criminal, money-laundering, and a criminal conspiracy to violate campaign finance laws.
It now seems to closely-watching observers that the kid (Bankman-Fried) burned his own company -- and his own ass -- just to make sure the Dems won the mid-term elections, and seems to have done it by pulling the rug out from all those that had funds there in FTX.
So the collapse of FTX is now linked not only to Ukraine, but also to US Democrat politicians who got money from Sam Bankman-Fried, to campaign for the just-ended elections!
UPDATED 7:33 AM SUNDAY -- UKRAINE "MILITARY AID" FROM USA --- WAS INVESTED IN CRYPTO "FTX" BY UKRAINE!
The sudden collapse of crypto exchange
Ukraine Partners With FTX, Everstake to Launch New Crypto Donation Website
March 15, 2022The Ukrainian government launched a new crypto donations website on Monday, streamlining its multimillion-dollar effort to turn bitcoin into bullets, bandages and other war materiel.
“Aid for Ukraine,” which has the backing of crypto exchange FTX, staking platform Everstake and Ukraine’s Kuna exchange, will route donated crypto to the National Bank of Ukraine, Everstake’s Head of Growth Vlad Likhuta told CoinDesk. Ukraine’s crypto-savvy Ministry of Digital Transformation is also involved.
The country's collective efforts have already raised some $48 million in bitcoin (BTC), DOT, ether (ETH), SOL, tether (USDT) and other cryptocurrencies, according to the website. Other estimates place the amount closer to $100 million, but totals vary with market swings and exactly which websites are included.
The website deepens an unprecedented tie-up between public and private sector forces in crypto. FTX is converting donations into fiat for deposit at the National Bank of Ukraine, a press release said. It described this relationship as a “first.”
Everstake’s involvement allows more cryptocurrencies to be accepted by the website.
The central bank is using donations to support “humanitarian aid programs” as well as Ukraine's armed forces, according to the website. “The people will continue their fight for freedom, but they need more ammunition and necessities,” the website read.
“Crypto assets proved extremely helpful in facilitation of funding flows to Ukrainian citizens and soldiers, as well as in raising awareness and engaging people worldwide,” Oleksandr Bornyakov, an official at the digital ministry, said in a statement.
He hinted that an upcoming NFT collection “will give the next boost to the crypto fundraising process.”

Ukraine Partners With FTX, Everstake to Launch New Crypto Donation Website
FTX is converting crypto contributions to Ukraine’s war effort into fiat for deposit at the National Bank of Ukraine.

@Anmdt @Cabatli_TR @TR_123456 @Mis_TR_Like @Test7 @Yasar @Zafer @Combat-Master @TheInsider @Stimpy75 @Stuka @OPTIMUSUkraine Partners With FTX, Everstake to Launch New Crypto Donation Website
March 15, 2022
The Ukrainian government launched a new crypto donations website on Monday, streamlining its multimillion-dollar effort to turn bitcoin into bullets, bandages and other war materiel.
“Aid for Ukraine,” which has the backing of crypto exchange FTX, staking platform Everstake and Ukraine’s Kuna exchange, will route donated crypto to the National Bank of Ukraine, Everstake’s Head of Growth Vlad Likhuta told CoinDesk. Ukraine’s crypto-savvy Ministry of Digital Transformation is also involved.
The country's collective efforts have already raised some $48 million in bitcoin (BTC), DOT, ether (ETH), SOL, tether (USDT) and other cryptocurrencies, according to the website. Other estimates place the amount closer to $100 million, but totals vary with market swings and exactly which websites are included.
The website deepens an unprecedented tie-up between public and private sector forces in crypto. FTX is converting donations into fiat for deposit at the National Bank of Ukraine, a press release said. It described this relationship as a “first.”
Everstake’s involvement allows more cryptocurrencies to be accepted by the website.
The central bank is using donations to support “humanitarian aid programs” as well as Ukraine's armed forces, according to the website. “The people will continue their fight for freedom, but they need more ammunition and necessities,” the website read.
“Crypto assets proved extremely helpful in facilitation of funding flows to Ukrainian citizens and soldiers, as well as in raising awareness and engaging people worldwide,” Oleksandr Bornyakov, an official at the digital ministry, said in a statement.
He hinted that an upcoming NFT collection “will give the next boost to the crypto fundraising process.”

Ukraine Partners With FTX, Everstake to Launch New Crypto Donation Website
FTX is converting crypto contributions to Ukraine’s war effort into fiat for deposit at the National Bank of Ukraine.www.coindesk.com

This story is huge folks.
This can totally devastate the whole crypto currency ecosystem. How can there be any trust anymore. BITCOIN anchored itself at 16800 but I imagine it will be heading down to 12000 before long.@Anmdt @Cabatli_TR @TR_123456 @Mis_TR_Like @Test7 @Yasar @Zafer @Combat-Master @TheInsider @Stimpy75 @Stuka @OPTIMUS
This story is huge folks.
People's Republic of China State-Sponsored Cyber Actor Living off the Land to Evade Detection
Summary The United States and international cybersecurity authorities are issuing this joint Cybersecurity Advisory (CSA) to highlight a recently discovered cluster of activity of interest associated with a People’s Republic of China (PRC) state-sponsored cyber actor, also known as Volt Typhoon. Private sector partners have identified that this activity affects networks across U.S. critical infrastructure sectors, and the authoring agencies believe the actor could apply the same techniques against these and other sectors worldwide.
This advisory from the United States National Security Agency (NSA), the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the U.S. Federal Bureau of Investigation (FBI), the Australian Signals Directorate’s Australian Cyber Security Centre (ACSC), the Communications Security Establishment’s Canadian Centre for Cyber Security (CCCS), the New Zealand National Cyber Security Centre (NCSC-NZ), and the United Kingdom National Cyber Security Centre (NCSC-UK) (hereafter referred to as the “authoring agencies”) provides an overview of hunting guidance and associated best practices to detect this activity.
One of the actor’s primary tactics, techniques, and procedures (TTPs) is living off the land, which uses built-in network administration tools to perform their objectives. This TTP allows the actor to evade detection by blending in with normal Windows system and network activities, avoid endpoint detection and response (EDR) products that would alert on the introduction of third-party applications to the host, and limit the amount of activity that is captured in default logging configurations. Some of the built-in tools this actor uses are: wmic, ntdsutil, netsh, and PowerShell.
Volt Typhoon targets US critical infrastructure with living-off-the-land techniques
Microsoft has uncovered stealthy and targeted malicious activity focused on post-compromise credential access and network system discovery aimed at critical infrastructure organizations in the United States. The attack is carried out by Volt Typhoon, a state-sponsored actor based in China that typically focuses on espionage and information gathering. Microsoft assesses with moderate confidence that this Volt Typhoon campaign is pursuing development of capabilities that could disrupt critical communications infrastructure between the United States and Asia region during future crises.Volt Typhoon has been active since mid-2021 and has targeted critical infrastructure organizations in Guam and elsewhere in the United States. In this campaign, the affected organizations span the communications, manufacturing, utility, transportation, construction, maritime, government, information technology, and education sectors. Observed behavior suggests that the threat actor intends to perform espionage and maintain access without being detected for as long as possible.

Volt Typhoon targets US critical infrastructure with living-off-the-land techniques | Microsoft Security Blog
Microsoft has uncovered stealthy malicious activity by Volt Typhoon focused on post-compromise credential access & network system discovery.
www.microsoft.com
U.S. Hunts Chinese Malware That Could Disrupt American Military Operations
The Biden administration is hunting for malicious computer code it believes China has hidden deep inside the networks controlling power grids, communications systems and water supplies that feed military bases in the United States and around the world, according to American military, intelligence and national security officials.
The discovery of the malware has raised fears that Chinese hackers, probably working for the People’s Liberation Army, have inserted code designed to disrupt U.S. military operations in the event of a conflict, including if Beijing moves against Taiwan in coming years.
The malware, one congressional official said, was essentially “a ticking time bomb” that could give China the power to interrupt or slow American military deployments or resupply operations by cutting off power, water and communications to U.S. military bases. But its impact could be far broader, because that same infrastructure often supplies the houses and businesses of ordinary Americans, according to U.S. officials.
The first public hints of the malware campaign began to emerge in late May, when Microsoft said it had detected mysterious computer code in telecommunications systems in Guam, the Pacific island with a vast American air base, and elsewhere in the United States.
More than a dozen U.S. officials and industry experts said in interviews over the past two months that the Chinese effort predated the May report by at least a year, and that the U.S. government’s effort to hunt down the code, and eradicate it, has been underway for some time. Most spoke on the condition of anonymity to discuss confidential and in some cases classified assessments.
They say the Chinese effort appears more widespread — in the United States and at American facilities abroad — than they had initially realized. But officials acknowledge that they do not know the full extent of the code’s presence in networks around the world.
The discovery of the malware has touched off a series of Situation Room meetings in the White House in recent months, as senior officials from the National Security Council, the Pentagon, the Homeland Security Department and the nation’s spy agencies attempt to understand the scope of the problem and plot a response.
Biden administration officials have begun to brief members of Congress, some state governors and utility companies about the findings, and confirmed some conclusions about the operation in interviews with The New York Times.
There is a debate inside the administration over whether the goal of the operation is primarily aimed at disrupting the military, or at civilian life more broadly in the event of a conflict. But officials say that the initial searches for the code have focused first on areas with a high concentration of American military bases.
In response to questions from The Times, the White House issued a statement Friday night that made no reference to China or the military bases.
“The Biden administration is working relentlessly to defend the United States from any disruptions to our critical infrastructure, including by coordinating interagency efforts to protect water systems, pipelines, rail and aviation systems, among others,” said Adam Hodge, the acting spokesman for the National Security Council.
He added: “The president has also mandated rigorous cybersecurity practices for the first time.” Mr. Hodge was referring to a series of executive orders, some motivated by concerns over SolarWinds, commercial software used widely by the U.S. government that was breached by a Russian surveillance operation, and the Colonial Pipeline ransomware attack by a Russian criminal group. That attack resulted in the temporary cutoff of half the gasoline, jet fuel and diesel supplies that run up the East Coast.
The U.S. government and Microsoft have attributed the recent malware attack to Chinese state-sponsored actors, but the government has not disclosed why it reached that conclusion. There is debate among different arms of the U.S. government about the intent of the intrusions, but not about their source.
The public revelation of the malware operation comes at an especially fraught moment in relations between Washington and Beijing, with clashes that include Chinese threats against Taiwan and American efforts to ban the sale of highly sophisticated semiconductors to the Chinese government.
The discovery of the code in American infrastructure, one of Mr. Biden’s most senior advisers said, “raises the question of what, exactly, they are preparing for — or whether this is signaling.”
If gaining advantage in a Taiwan confrontation is at the heart of China’s intent, tabletop exercises conducted by the government, think tanks and other outside experts suggest time is of the essence. Slowing down American military deployments by a few days or weeks might give China a window in which it would have an easier time taking control of the island by force.
Chinese concern about American intervention was most likely fueled by President Biden’s several statements over the past 18 months that he would defend Taiwan with American troops if necessary.
Another theory is that the code is intended to distract. Chinese officials, U.S. intelligence agencies have assessed, may believe that during an attack on Taiwan or other Chinese action, any interruptions in U.S. infrastructure could so fixate the attention of American citizens that they would think little about an overseas conflict.
Chinese officials did not respond to requests for comment concerning the American discovery of the code. But they have repeatedly denied conducting surveillance or other cyberoperations against the United States.
They have never conceded that China was behind the theft of security clearance files of roughly 22 million Americans — including six million sets of fingerprints — from the Office of Personnel Management during the Obama administration. That exfiltration resulted in an agreement between President Obama and President Xi Jinping that resulted in a brief decline in malicious Chinese cyberactivity. The agreement has since collapsed.
Now, Chinese cyberoperations seem to have taken a turn. The latest intrusions are different from those in the past because disruption, not surveillance, appears to be the objective, U.S. officials say. At the Aspen Security Forum last week, Rob Joyce, the director of cybersecurity at the National Security Agency, said China’s recent hack targeting the American ambassador to Beijing, Nicholas Burns, and the commerce secretary, Gina Raimondo, was traditional espionage. But he said the intrusions in Guam were “really disturbing” because of their disruptive potential.
The Chinese code, the officials say, appears directed at ordinary utilities that serve both civilian populations and nearby military bases. Only America’s nuclear sites have self-contained communication systems, electricity and water pipelines. (The code has not been found in classified systems. Officials declined to describe the unclassified military networks in which the code has been found.)
While the most sensitive planning is carried out on classified networks, the military routinely uses unclassified, but secure, networks for basic communications, personnel matters, logistics and supply issues.
Officials say that if the malware is activated, it is not clear how effective it would be at slowing an American response — and that the Chinese government may not know, either. In interviews, officials said they believe that in many cases the communications, computer networks and power grids could be quickly restored in a matter of days.
But intelligence analysts have concluded that China may believe there is utility in any disruptive attack that could slow down the U.S. response.
The first hints of the new campaign by China came in May, when experts at Microsoft released some details of the malware found in Guam — home to major U.S. Air Force and Marine bases — and elsewhere in the United States. The company attributed the intrusion to a Chinese state-sponsored hacker the experts called Volt Typhoon.
A warning from the Homeland Security Department’s Cybersecurity and Infrastructure Security Agency, the National Security Agency and others issued the same day said the state-sponsored hacker was able to avoid detection by blending its attack in with normal computer activity but did not outline other details of the threat.
Officials briefly considered whether to leave the malware in place, quietly monitor the code they had found and prepare plans to try to neutralize it if it was even activated. Monitoring the intrusions would allow them to learn more about it, and possibly lull the Chinese hackers into a false sense that their penetration had not been exposed.
But senior White House officials quickly rejected that option and said that given the potential threat, the prudent path was to excise the offending malware as quickly as it could be found.
Still, there are risks.
American cybersecurity experts are able to remove some of the malware, but some officials said there are concerns that the Chinese could use similar techniques to quickly regain access.
Removing the Volt Typhoon malware also runs the risk of tipping off China’s increasingly talented hacking forces about what intrusions the United States is able to find, and what it is missing. If that happens, China could improve its techniques and be able to reinfect military systems with even harder-to-find software.
The recent Chinese penetrations have been enormously difficult to detect. The sophistication of the attacks limits how much the implanted software is communicating with Beijing, making it difficult to discover. Many hacks are discovered when experts track information being extracted out of a network, or unauthorized accesses are made. But this malware can lay dormant for long periods of time.
Speaking earlier this month at an intelligence summit, George Barnes, the deputy director of the National Security Agency, said the Volt Typhoon attacks demonstrated how much more sophisticated China had become at penetrating government and private sector networks.
Mr. Barnes said that rather than exploit flaws in software to gain access, China had found ways to steal or mimic the credentials of system administrators, the people who run computer networks. Once those are in hand, the Chinese hackers essentially have the freedom to go anywhere in a network and implant their own code.
“China is steadfast and determined to penetrate our governments, our companies, our critical infrastructure,” Mr. Barnes said.
“In the earlier days, China’s cyberoperations activities were very noisy and very rudimentary,” he continued. “They have continued to bring resources, sophistication and mass to their game. So the sophistication continues to increase.”

U.S. Hunts Chinese Malware That Could Disrupt American Military Operations (Published 2023)
American intelligence officials believe the malware could give China the power to disrupt or slow American deployments or resupply operations, including during a Chinese move against Taiwan.
Pentagon hit by ‘critical compromise’ of US air force communications – report
The Pentagon is investigating a “critical compromise” of communications across 17 US air force facilities, according to reports.
The US department of defense’s investigation comes amid a tip from a base contractor that a 48-year-old engineer at the Arnold air force base in Tennessee had taken home various government radio technologies, Forbes first reported Friday.
According to a search warrant obtained by investigators and reviewed by Forbes, the equipment allegedly taken by the engineer cost nearly $90,000. It also added that when law enforcement agents searched his home, they found that he had “unauthorized administrator access” to radio communication technology used by the Air Education and Training Command (AETC), which is one of the nine major commands of the air force and in turn affected 17 defense department installations.
I was a US nuclear missile operator. I’m grateful for the Oppenheimer film
Read more
Investigators also found an open computer screen that showed the engineer running a Motorola radio programming software. According to the warrant, the software “contained the entire Arnold air force base (AAFB) communications system,” Forbes reported.
The outlet also reported that, according to the warrant, a document detailing the forensics on technologies seized from the engineer’s home revealed that he had a USB which contained “administrative passwords and electronic system keys” for the AETC radio network.
Other items seized included flash drives that contained “local law enforcement radio programming files” and “Motorola radio programming files” which presented a warning banner that indicated they were government property.
Installer files which were recovered in the search opened with a “CONFIDENTIAL RESTRICTED” pop-up, according to Forbes.
The warrant also recounted how witnesses and co-workers informed investigators that the engineer had allegedly “sold radios and radio equipment, worked odd hours, was arrogant, frequently lied, displayed inappropriate workplace behavior and sexual harassment, had financial problems, and possessed [Arnold air force base land mobile radio] equipment”.
It added that a colleague had reported him twice due to “insider threat indicators” as well as unauthorized possession of air force equipment, according to investigators.
Investigators also reported to have found evidence which indicated that the searched contractor had possible access to FBI communications, as well as Tennessee state agencies, Forbes reported. The FBI is working alongside the air force on the investigation, according to the outlet.
Forbes has not yet disclosed the engineer’s name as he has not been charged. However, the outlet reported that according to his LinkedIn page, the engineer has an extensive history in cybersecurity and radio communications.
“He claims to have carried out numerous tests of the Arnold air force base’s security, improved protection of radio communications on the site and had knowledge of the encryption used on government data,” Forbes reported.
The Forbes report comes only three months after one of the worst leaks in US intelligence in over a decade. In that case, 21-year-old Jack Teixeira, an air national guardsman at the time, was arrested on suspicion of leaking hundreds of Pentagon documents.
He has since been charged under the Espionage Act.
In another potential security issue facing the government, the New York Times reported Saturday that the Joe Biden White House was hunting alleged Chinese malware that it believes is hidden across various American facilities.
The malware is a “ticking time bomb” that could allow China to interrupt or hinder American military deployments by cutting off power, water and various communication channels to US military bases, according to one congressional official speaking to the New York Times.
The outlet also reports that more than a dozen government officials and experts said the government effort to track down and eliminate the malware has been “underway for some time,” although the full extent of the code’s presence across various networks remains unknown due to how deeply it is hidden.
In a statement to the New York Times, a National Security Council spokesperson said that the Biden administration was “working relentlessly to defend the United States from any disruptions to our critical infrastructure, including by coordinating interagency efforts to protect water systems, pipelines, rail and aviation systems, among others”.

Pentagon hit by ‘critical compromise’ of US air force communications – report
Forbes reports claim that engineer at Arnold air force base in Tennessee had taken home government radio technologies
A thread about the cyber-espionage capabilities of Apple products.
Chuck your iPhones into the bin, they're spying on you.
The US intelligence services NSA and CIA have been tapping iPhones in Russia since 2019!
And is it just Russia? I think the whole world!
First the Russian intelligence service FSB, then Kaspersky's technical analysis was published.
Some of the findings are suspicious.
Chuck your iPhones into the bin, they're spying on you.